The Power of the NIST Cybersecurity Framework: Identify, Protect, Detect, Respond, and Recover
3 min read
How to Use NIST to Navigate Cybersecurity
With increasing cyber threats, businesses must stay vigilant and proactive. Cybersecurity frameworks like the one by the National Institute of Standards and Technology (NIST) offer a structured way to deal with these dangers. Let’s look at the five main functions: Identify, Protect, Detect, Respond, and Recover.
- Identify: Knowing the state of your cyber security is critical. Identification is the first step toward a strong protection plan. In this process, you look at your systems, assets, data, and skills to figure out what risks might be there. It involves making a thorough map of your digital infrastructure and figuring out the weak spots that could be used by hackers. It also involves deciding what data is absolutely critical and what is important. All data and all systems are not created equal. For most businesses, their accounting systems and emails are considered critical, while an individual’s personal laptop may simply be considered important, but not critical to business operations. Understanding your entire data architecture is a critical first step to take when going to the next phases of the NIST cybersecurity framework.
- Protect: Putting up strong defenses to keep out intruders is the next step. Once you know what risks might happen, the next step is to protect your assets. At this stage, the right safeguards are put in place to make sure that vital infrastructure services keep running. Access control, data security, and methods and procedures for protecting information can all be used as protective measures.
- Detect: There is always a chance of getting into your network, no matter how strong your defenses are. Here is where the detection part comes in. By putting in place continuous monitoring, you can find cybersecurity events quickly. Early discovery can cut down on the damage and downtime that could be caused by a breach.
- Respond: Even if you try to find, protect, and detect cybersecurity events, they can still happen. When they do, it’s important to act quickly and effectively. In this step, a plan is made for how to deal with the effects of a hacking event. It also means talking to people who have a stake in the situation and coordinating a quick reaction to reduce the damage.
- Recover: Recovery isn’t just about getting back to normal. It’s about learning from what happened, getting back any capabilities or services that were lost because of a cybersecurity event, and making changes to processes to stop it from happening again. This could mean making changes to security and detection tools and making response plans stronger.
Why it’s important to have a complete cybersecurity framework
The NIST hacking Framework is a way to deal with hacking risks in a whole-person way. By using the Identify, Protect, Detect, Respond, and Recover approach, companies can be better prepared to deal with cyber threats and can recover faster after a breach.
Get Novatech to protect your business
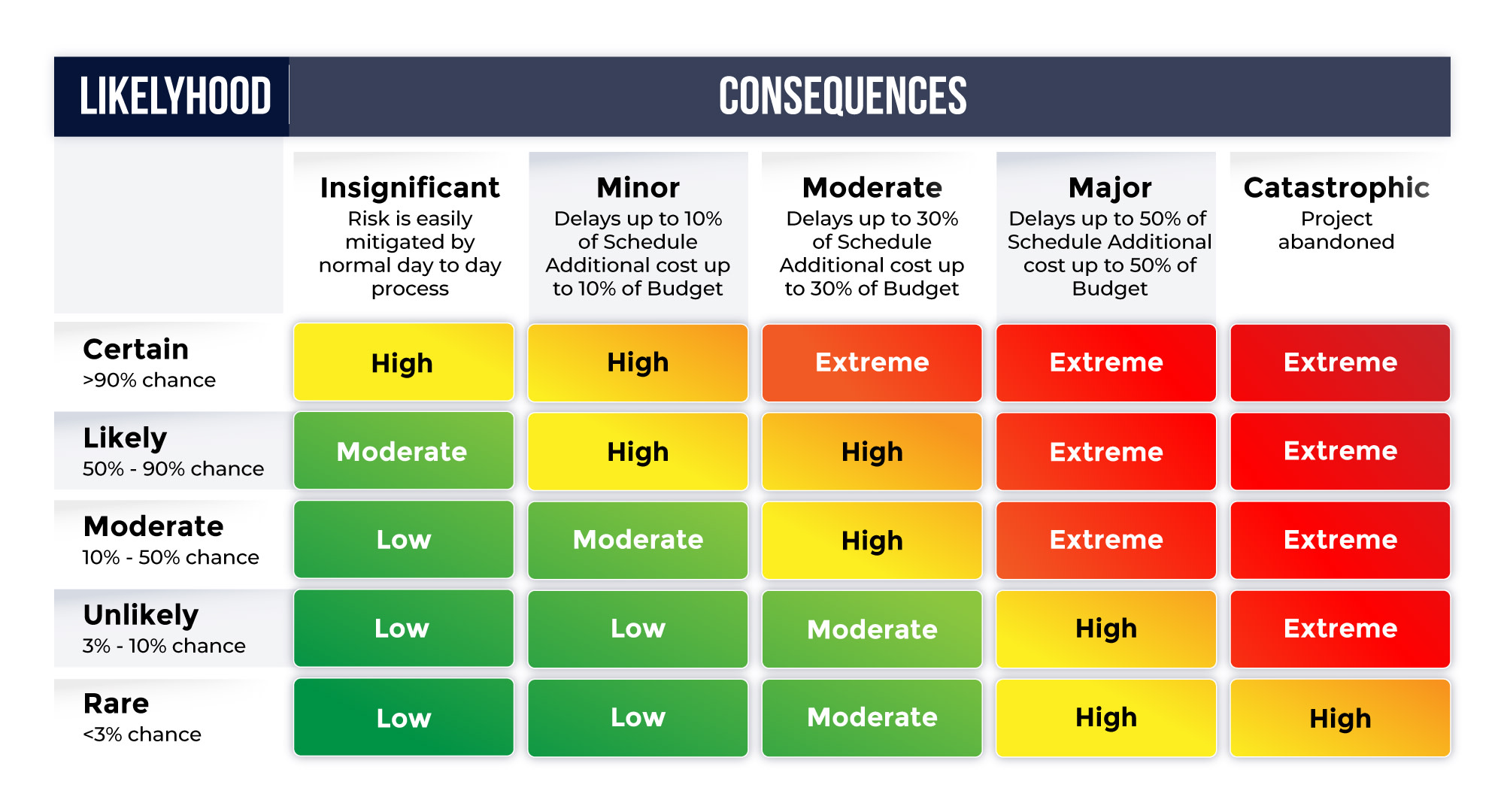
You want to use the NIST Cybersecurity Framework but don’t know where to start. Novatech can help you. Our cybersecurity experts will work with you to find risks, protect your assets, find threats, respond to incidents, and recover successfully. Contact us today for a free risk review and take your business’s first step toward a safer future. In the first step, we will be working on the “identify” phase of risk assessment and management. This report will help you understand the possible risks to your systems and business so you can decide the importance of each threat as all data is not created equal. Schedule an appointment to talk to one of our security specialists today.